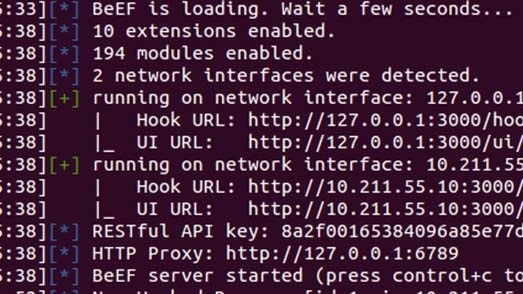
BeEF The Browser Exploitation Framework v0.4.3.7 released

 BeEF is short for The Browser Exploitation Framework. It is a penetration testing tool that focuses on the web browser.Amid growing concerns about web-borne attacks against clients, including mobile clients, BeEF allows the professional penetration tester to assess the actual security posture of a target environment by using client-side attack vectors.
BeEF is short for The Browser Exploitation Framework. It is a penetration testing tool that focuses on the web browser.Amid growing concerns about web-borne attacks against clients, including mobile clients, BeEF allows the professional penetration tester to assess the actual security posture of a target environment by using client-side attack vectors.
Unlike other security frameworks, BeEF looks past the hardened network perimeter and client system, and examines exploitability within the context of the one open door: the web browser. BeEF will hook one or more web browsers and use them as beachheads for launching directed command modules and further attacks against the system from within the browser context.
Unlike other security frameworks, BeEF focuses on leveraging browser vulnerabilities to assess the security posture of a target. This project is developed solely for lawful research and penetration testing.
BeEF hooks one or more web browsers as beachheads for the launching of directed command modules. Each browser is likely to be within a different security context, and each context may provide a set of unique attack vectors.
Changes
- Twitter and E-mail notifications (thanks @marcwickenden): we have a new extension where you can configure an SMTP server or Twitter account in order to receive automatic notifications as soon as a new browser is hooked in BeEF;
- HTTPS support (thanks to one of our long-term developers, Christian @xntrik Frichot): you can now start BeEF with full HTTPS support. You should use this when you want to target HTTPS applications, especially if the user is using latest Chrome/Firefox browsers: they do security checks for mixed content and prevent the hook to work in case you use HTTP;
- new Chrome extension module (thanks Mike Haworth): now you can have screenshots of the current tab the user is in;
- Gmail phishing and Flash Webcam modules (thanks floyd.ch): using the first module you can logout a user from Gmail, create a fake Gmail login page, then steal the the Google account credentials. With the second module, if the user clicks “Allow Webcam” from the popup created by Flash, you can get photos from his webcam at a defined time interval you can specify;
- Nat_pinning module (thanks Bart Leppens): you probably remember Samy’s research on the topic. Well, we added this nice attack to BeEF, so you can have fun with it.
- The GlassFish exploit has been enhanced (again, thanks Bart), and we also added GlassFish fingerprinting to our internal network fingerprinting module.
- Brendan @_bcoles Coles, as always, did a great job adding new modules and porting various attacks to BeEF: Spring exploit for CVE-2010-1622, lots of XSRF and some RCE modules for various embedded devices like routers and cameras (D-Link dir-615, Linksys wcv series, Cisco E2400, 3Com OfficeConnect ADSL Wireless 11g, Asmax AR-804gu). Other than that, he also added enhanced fingerprinting for various mobile devices, and the balloon dialogs for the admin web-gui. Let us know via @beefproject if you want more/different stuff in this dialog.
- Michele @antisnatchor Orru, except from bugfixes, added the confirm_close_tab module, in order to achieve better hook persistence and annoy the user (basically the user is asked for confirmation – in a loop – when he’s closing the hooked tab). Another bunch of changes he worked on were about the AssetHandler (you can now bind/unbind raw sockets in BeEF, useful for example in the nat_pinning module to bind a socket on port 6667), the RESTful API (added a /api/modules/multi endpoint that you can now use to launch multiple modules at once to a single target) and the admin web-gui (added a JSON endpoint that enables you to call the RESTful API from ExtJS)
More information: here





